Extract Forensic Data From Computers With OSForensics
Rainbow tables are pre-computed tables, used for reversing cryptographic hash functions, which are often used for cracking password hashes. Computers which rely on password authentication require a mechanism to determine if the entered password is correct. One can store a cryptographic hash of the password to protect the stored information because such hashes are difficult to reverse.
OSForensics enables you to use Rainbow Tables to retrieve passwords, provided you have the hash of that password. The use of rainbow tables serve as a time-memory trade off in the decryption of a hash. With OSForensics you can also recoverybrowser passwords, aggregate and organize results and case items, analyze systems main memory, CPU, USB and hard drive information, uncover the user actions performed recently on the system, create an index of the files on a hard disk, look up files quicker than Windows default functionality, and much more. The main interface contains multiple tabs and sub-categories which contain options to perform the aforementioned tasks.
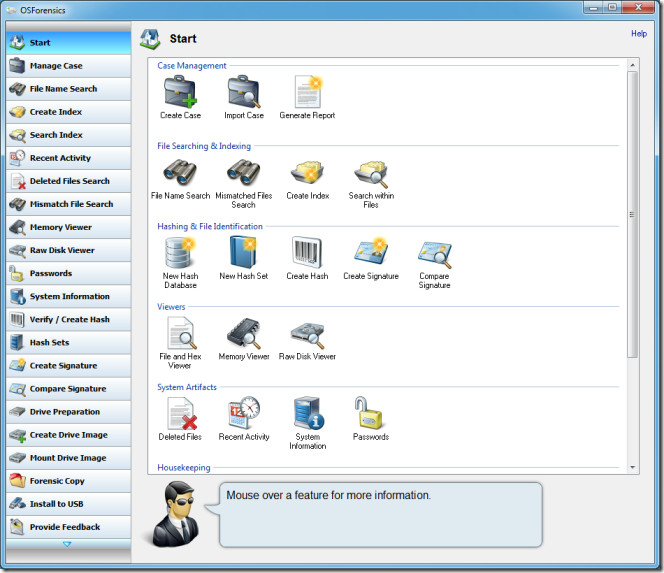
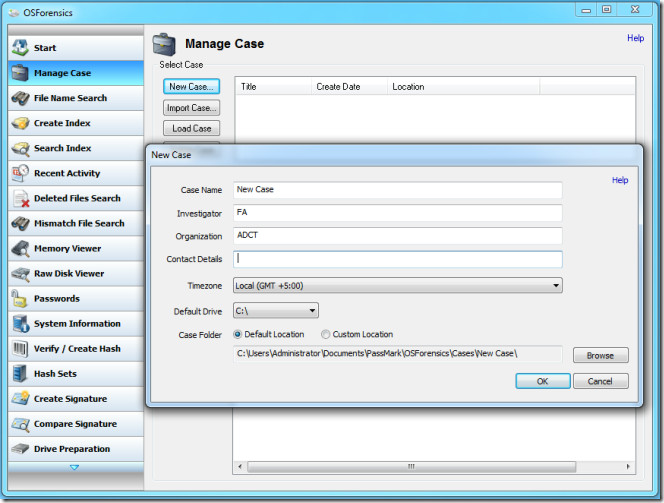
You can create a case from the Create Case option in the Start tab to group together all findings from different features of OSFForensics. Once done, you can manage the case from the manage case tab and perform filename search, create and index and search indexes from the following three tabs. OSForensics can also search the content of files and return results after indexing. It is able to search within most common file formats.
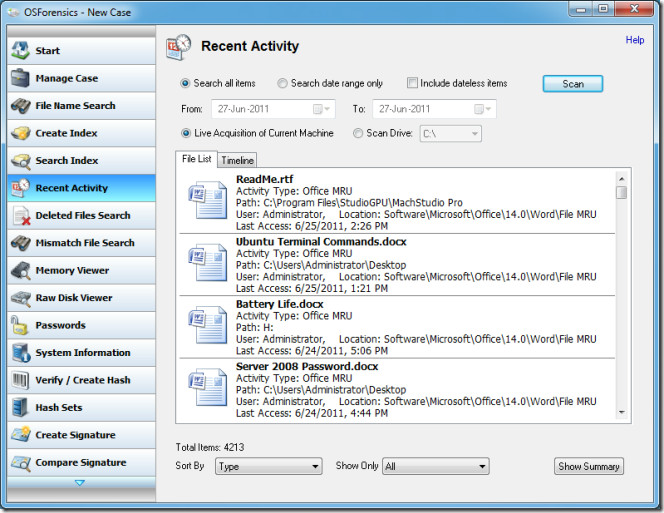
To view a log of recent user activity, head over to the Recent Activity tab and click on Scan. This will display a list of recently accessed files, application and performed functions. You can refine your search according to date, time type, and use the filter options to view files by most recently used, WLAN, USB, browser history, downloads, chat log and cookies. Likewise, The Deleted Files Search tab allows searching for deleted files.
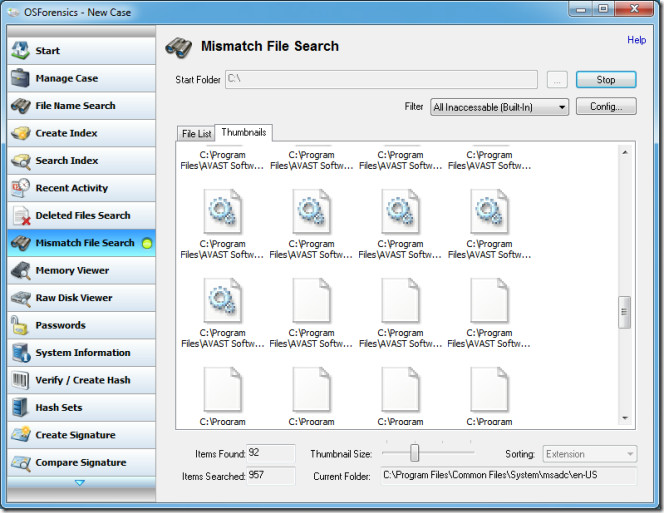
From the Mismatch Files Search tab, you can locate Default (Built in), Mismatched (Built in), and all built in files. You can refine thumbnail view size from the slider at the bottom and use the sorting option to sort files by extension, name, folder, size and mismatch type.
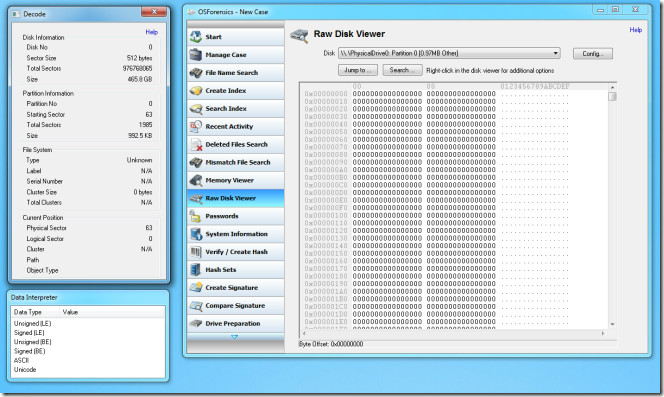
Raw memory and disk information can be retrieved from the Raw Memory and Raw Disk tabs. This can be useful for checking for hard disk, partition, file system and current position information. The Raw Memory tab allows retrieving dump process, crash dump files, and physical memory content.
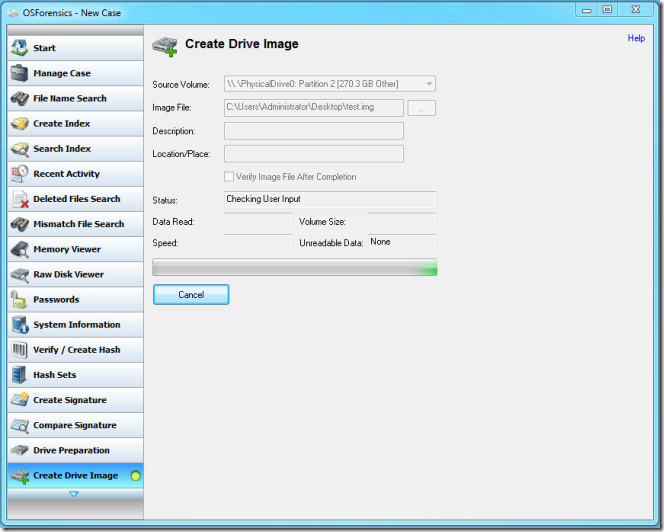
OSForencis also allows creating drive images which can be later mounted from the Mount Drive Image tab.
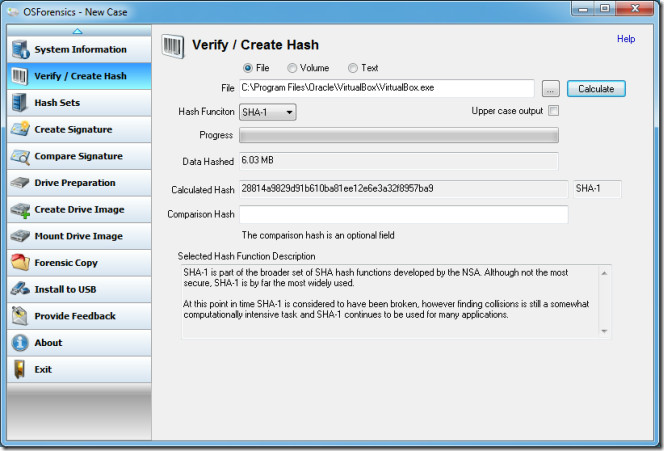
Perhaps the most important function which OSForensics perform is its ability to create a unique digital identifier for a file or disk volume by calculating its hash value using the Verify/Create Hash module in OSForensics. You can choose from a number of cryptographic algorithms to create a hash, such as SHA-1, MD5 and SHA-256. Hash values uniquely identify the contents of a file and can be used to discover other files with the same content, regardless of differing file name or file extension. This can be achieved from the Verify/Create hash and Hash Sets tabs.
To learn more about using the features of OSForencis you can visit the developers website to understand the procedure and utility of the above mentioned feature in more detail. OSForencis works on Windows XP, Windows Vista and Windows 7.
