How To Identify A Fake Google Login Form [Chrome]
Phishing attacks are getting smarter so that it’s hard for even the most diligent user to be able to identify one. Sometimes, the attack occurs and people are none the wiser until it’s too late. Other times, security experts are able to identify a potential phishing scam before it even happens like the fake Apple sign in prompt. Because phishing scams often target large, popular services, these services also try to protect its users from these scams. Google has released a Chrome extension called Password Alert that can identify a fake Google login form.
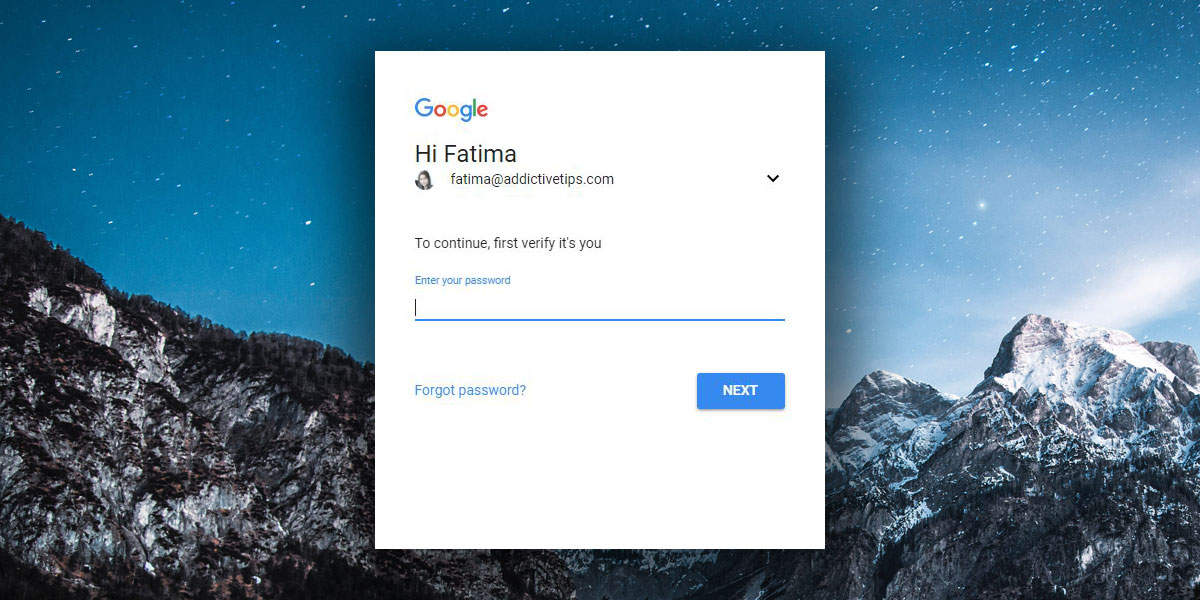
Identify A Fake Google Login Form
Install Password Alert and that’s really all you have to do. The extension adds an icon next to the URL bar but it won’t show you anything if the Google login form you enter your credentials into is the real thing. The extension only tells you if you’ve entered your login information in a fake Google login form.
This year, there were quite a few high profile phishing scams. One targeted Google Docs users, while another claimed affiliation with Plex.
In the case of the Google Docs phishing attack, Google was quick to respond to it. The problem was fixed within a matter of hours of it being reported on Reddit. That particular scam didn’t need to ask you to login again i.e. there was no extra verification step. It did ask for additional permission to access information in your account. This extension probably would not have been able to save you in that case but it’s a good layer of security to have in your browser.
Room For Improvement
Password Alert is reactive, not proactive. According to its Chrome Web Store description, the extension warns you about potential danger only after you have entered your email and password in a fake Google login form. The extension doesn’t actively scan webpages you visit to check if they’re real or not.
What this means is that by the time Password Alert warns you that you’ve been phished, you will already have given up your login credentials. The extension will prompt you to change your login and password right away, which you should. The idea is that the extension will be able to alert you fast enough so that even if your information has been compromised, the attackers don’t have enough time to use it before you’re able to reset it.
That’s an optimistic approach but the problem is that people tend to use the same password, or a variation of it across multiple services. An unsuspecting user might assume changing their Google login credentials will be enough. A more diligent user will need to quickly change their password across multiple services before it can be misused and it’s likely going to be a race against time.

Google Login