6 Best ITIL Security Management Tools in 2026
ITIL is a relatively widespread and very thorough framework for IT service management. Originally from the UK and designed to serve both the government and private businesses, it is a set of highly structures processes, recommendations and practices. It is separated into several specific areas with security management being nothing more than one of many aspects of it. But since security is such an important topic—especially when considering the modern threat scene and how organizations are constantly being targeted by unscrupulous hackers—we’ve decided to have a look at some of the very best ITIL security management tool.
We’ll start off by explaining in greater details what ITIL is before moving on to the specific area of ITIL security management. Next, we’ll introduce the concept of Security Information and Event Management, describe what it consists of, and explain how it can relate to ITIL security management. We’ll finally get to the interesting part and present a quick review of some of the best ITIL security management tool, describing each tool’s best features and functionality.
ITIL In A Nutshell
ITIL, which used to stand for Information Technology Infrastructure Library, started way back in the 80s as an effort from the UK Government’s Central Computer and Telecommunications Agency (CCTA) to develop a set of recommendations and standard practices for IT service management in the government and the private sector as well. It originated as a collection of books, each covering a specific practice within IT service management and was built around a process model-based view of controlling and managing operations.
Initially composed of over 30 volumes, it was later somewhat simplified and services were grouped, reducing the number of volumes to 5. It is still in constant evolution and the latest version’s Foundation book was published last February, ITIL groups various elements of IT service management into practices, with ITIL Security Management being just one of many.
About ITIL Security Management
As for the Security Management ITIL process, it “describes the structured fitting of information security in the management organization.” It is largely based on the code of practice for information security management system (ISMS) now known as ISO/IEC 27001.
The main goal of security management is, obviously, to ensure adequate information security. And in turn, the primary goal of information security is to protect information assets against risks, Thereby maintaining its value to the organization. Typically, this is expressed in terms of ensuring its confidentiality, integrity and availability, but also with related properties or goals such as authenticity, accountability, non-repudiation and reliability.
There are two primary aspects of security management. First and foremost are the security requirements which could either be defined within service level agreements (SLA) or other requirements specified in contracts, legislation as well as internal or external policies. The second aspect of it is simply basic security that guarantees management and service continuity. It is somewhat related to the first aspect as it is necessary to achieve simplified service-level management for information security.
While ITIL security management is a broad concept, it is somewhat more circumscribed in the context of software tools. When talking about security management tools, several types of tools can come to mind. One type, however, seems to be more interesting than the others: Security Information and Event Management (SIEM) tools.
Introducing Security Information and Event Management (SIEM)
In its simplest form, Security Information and Event Management is the process of managing security information and events. Concretely, a SIEM system does not provide any real protection. This is different, for instance, from anti-virus software which actively stops viruses from infecting protected systems. SIEM’s primary purpose is to make the life of network and security administrators easier. A typical SIEM system simply collects information from various systems—including network devices and other detection and protection systems. It then correlates all this information, assembling related events, and reacts to meaningful events in various ways. SIEM systems also include some form of reporting and, more importantly, dashboards and alerting subsystems.
What’s in a SIEM System
SIEM systems vary greatly from vendor to vendor. There are, however, a certain number of components to them that seem to be present in many of them. They won’t all include all of those components and, when they do, they could function differently. Let’s review some of the most important—and most common—components of SIEM systems in greater detail.
Log Collection And Management
Log collection and management is without a doubt the most important component of a SIEM system. Without it, there is no SIEM. The first thing a SIEM system has to do is acquire log data from a variety of different sources. It can either pull it—using, for instance, a locally installed agent—or different devices and systems can push it to the SIEM tool.
Since each system has its own way of categorizing and recording data, the next task of the SIEM tool is to normalize data and make it uniform, no matter what its source it is coming from. How that step is done varies mainly according to the original format of the received data.
Once it is normalized, the logged data will often be compared against known attack patterns in an attempt to recognize malicious behaviour as early as possible. Data can also be compared to previously collected data, thereby helping build a baseline that will further enhance abnormal activity detection.
Event Response
It is one thing to detect event but, once an event is detected, some response process must be started. This is what the event response module of the SIEM tool is all about. The event response can take many forms. In its most basic implementation, an alert message will be generated on the system’s dashboard. Email or SMS alerts can also be generated as the primary response.
However, the best SIEM systems go a step further and they can typically initiate some sort of remedial process. Again, this is something that can take many forms. The best systems have a complete incident response workflow system that can be customized, providing exactly the type of response you need. The incident response does not have to be uniform and different events—or different types of events—can trigger different processes. The top SIEM tools can give you complete control over the incident response workflow.
Reporting
It’s one thing to have log collection and management and to have an event response system in place, but you also need another important element: reporting. Even though you might not know it just yet, you will need reports; plain and simple. Your organization’s executives will need them to see for themselves that their investment in a SIEM system is paying off. But that’s not all, you might also need reports for conformity purposes. Complying with standards such as PCI DSS, HIPAA, or SOX is much easier when your SIEM system can generate conformity reports.
Reports may not be at the core of every SIEM system but they are still one of their essential components. Actually, reporting is one of the main differentiating factors between competing systems. Reports are like candies, you can never have too many. When evaluating systems, look at what reports are available and how they look like and keep in mind that the best systems will let you create custom reports.
Dashboard
The last important component of most SIEM tools is the dashboard. It is important as it is your window into the status of your SIEM system and, by extension, into the security of your IT environment. We could have said dashboards—with an S—just as well as there could be multiple dashboards available in some systems. Different people have different priorities and interests and the perfect dashboard for a network administrator will be different from that of a security administrator. Likewise, an executive will need a completely different dashboard as well.
While we can’t evaluate SIEM systems just on the number of dashboards they offer, you need to pick one that has the dashboard(s) you need. This is definitely something you’ll want to keep in mind as you evaluate vendors. And just like it is with reports, the best tools allow you to build customized dashboards to your liking.
Using SIEM As An ITIL Security Management Tool
No matter how complex the concept of security management can be in the context of the ITIL framework. It actually sums up to one primary goal: ensuring that data is secure. And although the whole IT security management paradigm has several different aspects, when it comes to the software tools you can use, there doesn’t appear to be an ITIL security management software package. On the other hand, there are countless offerings from various software publishers of tools aiming at ensuring the security of your data.
We’ve also seen how SIEM tools have a similar goal of preserving data security. It is, in our view, that common goal that makes them one of the best types of tools for IT security management. Keep in mind, however, that the practice of ITIL security management goes far beyond SIEM and, although they are a good starting point, they are only part of the solution, albeit an important one.
The Best ITIL Security Management Tools
Since we’ve established that the best ITIL security management tools were indeed SIEM tools, we’ve searched the market looking for the best of them. We found a great variety of tools from some of the best-known organizations. All of the tools on our list have all the major features you’d expect from a security management tool. Picking the best one for your particular need is often a matter of personal taste. Or perhaps one of the tools has a unique feature that appeals to you.
1. SolarWinds Security Event Manager (FREE TRIAL)
SolarWinds is a common name in the network monitoring world. Its flagship product, called the Network Performance Monitor is one of the best SNMP monitoring tool available. The company is also known for its numerous free tools such as its Advanced Subnet Calculator or its Free SFTP Server.
When it comes to SIEM, SolarWinds’ offering is the SolarWinds Security Event Manager. Formerly called the SolarWinds Log & Event Manager, the tool is best described as an entry-level SIEM tool. It is, however, one of the best entry-level systems on the market. The tool has almost everything you can expect from a SIEM system. This includes excellent log management and correlation features as well as an impressive reporting engine.
The tool also boasts excellent event response features which leave nothing to be desired. For instance, the detailed real-time response system will actively react to every threat. And since it’s based on behaviour rather than signature, you’re protected against unknown or future threats and zero-day attacks.
On top of its impressive feature set, the SolarWinds Security Event Manager’s dashboard is possibly its best asset. With its simple design, you’ll have no trouble finding your way around the tool and quickly identifying anomalies. Starting at around $4 500, the tool is more than affordable. And if you want to try it and see how it works in your environment, a free fully functional 30-day trial version is available for download.
2. Splunk Enterprise Security
Splunk Enterprise Security—or Splunk ES, as it is often called—is possibly one of the most popular SIEM systems. It is particularly famous for its analytics capabilities. Splunk ES monitors your system’s data in real-time, looking for vulnerabilities and signs of abnormal and/or malicious activity.
In addition to great monitoring, security response is another of Splunk ES’ strong suits. The system uses what Splunk calls the Adaptive Response Framework (ARF) which integrates with equipment from more than 55 security vendors. The ARF perform automated response, speeding up manual tasks. This will let you quickly gain the upper hand. Add to that a simple and uncluttered user interface and you have a winning solution. Other interesting features include the Notables function which shows user-customizable alerts and the Asset Investigator for flagging malicious activities and preventing further problems.
Splunk ES is truly an enterprise-grade product and that means that it comes with an enterprise-sized price tag. Pricing information is unfortunately not readily available from Splunk’s web site. You’ll need to contact the sales department to get a quote. Contacting Splunk will also allow you to take advantage of a free trial, should you want to try the product.
3. RSA NetWitness
Since 2016, NetWitness has focused on products supporting “deep, real-time network situational awareness and agile network response”. After being acquired by EMC which then merged with Dell, the NetWitness brand is now part of the RSA branch of the corporation. This is good news as RSA is a highly respected name in IT security.
RSA NetWitness is ideal for organizations seeking a complete network analytics solution. The tool integrates information about your organization which it uses to help prioritize alerts. According to RSA, the system “collects data across more capture points, computing platforms, and threat intelligence sources than other SIEM solutions”. The tool also features advanced threat detection which combines behavioral analysis, data science techniques, and threat intelligence. And finally, the advanced response system boasts orchestration and automation capabilities to help get rid of threats before they impact your business.
One of the main drawbacks of RSA NetWitness as reported by its user community is that it’s not the easiest to set up and to use. There is, however, comprehensive documentation available which can help you with setting up and using the product. This is another enterprise-grade product and, as it is often the case, you’ll need to contact sales to get pricing information.
4. ArcSight Enterprise Security Manager
ArcSight Enterprise Security Manager helps identify and prioritize security threats, organize and track incident response activities, and simplify audit and compliance activities. It used to be sold under the HP brand but ArcSight has now been merged into Micro Focus, another HP subsidiary.
Having been around for more than fifteen years, the ArcSight Enterprise Security Manager is another immensely popular SIEM tools. It compiles log data from various sources and performs extensive data analysis, looking for signs of malicious activity. To make it easy to identify threats quickly, the tool lets you view analysis results in real-time.
As for the product’s features, it leaves nothing to be desired. It has powerful distributed real-time data correlation, workflow automation, security orchestration, and community-driven security content. The ArcSight Enterprise Security Manager also integrates with other ArcSight products such as the ArcSight Data Platform and Event Broker or ArcSight Investigate. This is another enterprise-grade product and as such, pricing information is not readily available. It will require that you contact the ArcSight sales team to get a customized quote.
5. McAfee Enterprise Security Manager
McAfee is definitely another household name in the security industry. It is, however, better known for its virus protection line of products. Unlike other products in this list, the McAfee Enterprise Security Manager is not just software, it is an appliance that you can get either as a piece of hardware or in a virtual form.
In terms of its analytics capabilities, the McAfee Enterprise Security Manager is considered to be one of the best SIEM tools by many. The system collects logs across a wide range of devices and its normalization capabilities are second to none. The correlation engine easily compiles disparate data sources, making it easier to detect security events as they happen.
But to be true, there’s more to this McAfee solution than just its Enterprise Security Manager. To get a complete SIEM solution you also need the Enterprise Log Manager and Event Receiver. Fortunately, all products can be packaged in a single appliance. And for those of you who may want to try the product before you buy it, a free trial is available.
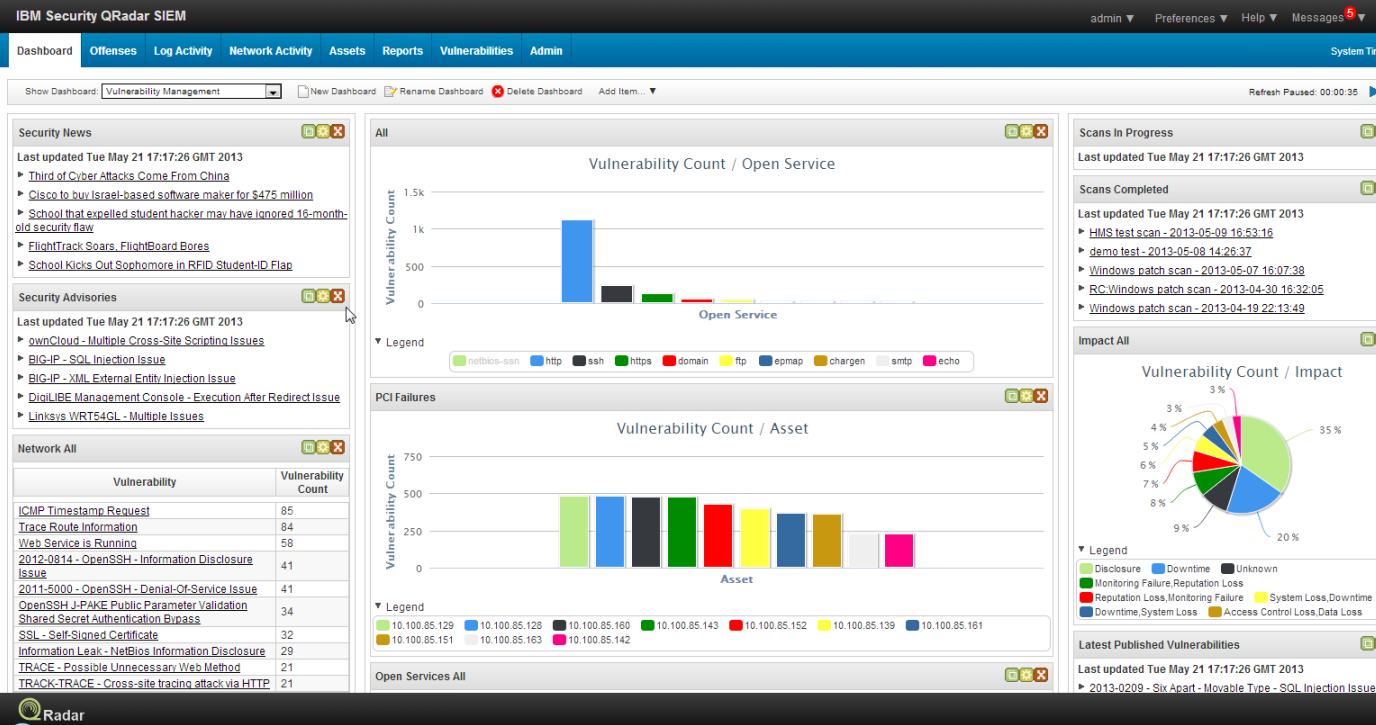
6. IBM QRadar
IBM is without a doubt one of the best-known names in the IT industry. It is no surprise then that the company has managed to establish its SIEM solution, IBM QRadar as one of the best products on the market. The tool empowers security analysts to detect anomalies, uncover advanced threats and remove false positives in real-time.
IBM QRadar boasts a suite of log management, data collection, analytics, and intrusion detection features. Together, they help keep your network infrastructure up and running. There is also risk modelling analytics that can simulate potential attacks.
Some of IBM QRadar’s key features include the ability to deploy the solution on-premises or in a cloud environment. It is a modular solution and one can quickly and inexpensively add more storage or processing power as their needs grow. The system uses intelligence expertise from IBM X-Force and integrates seamlessly with hundreds of IBM and non-IBM products.
IBM being IBM, though, you can expect to pay a premium price for its SIEM solution. But if you need one of the best SIEM tools on the market and a tool which is backed by a solid organization, IBM QRadar might very well be worth the investment.