How To Find Which App Is Using Your Webcam [Windows]
Controlling which apps can access your webcam is pretty simple in Windows 10. You can easily edit the list and revoke an app’s access to your webcam if you feel it isn’t safe. Windows 10 explicitly has you grant apps access to your webcam so you’re safe for the most part. Of course, this is for the good, trustworthy apps that have verified publishers or that come from the Windows Store. Apps that are malicious or that you might have unknowingly downloaded when downloading other apps are an entirely different story. If you suddenly find the little light next to your webcam turned On but can’t figure out which app is using it, there’s a very simple way to track it down. It requires an app called Process Explorer and the built-in Device Manager. Here’s what you need to do.
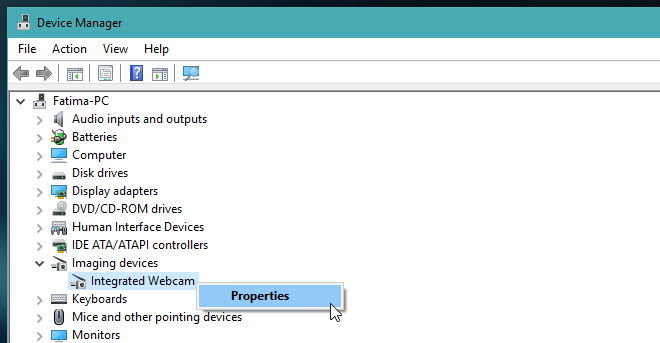
Run Device Manager and locate your webcam in the list of devices. It will likely appear in the Imaging Devices group but can be listed in a different group, depending on your hardware.
Find the webcam in Device Manager, right-click it, and select Properties.
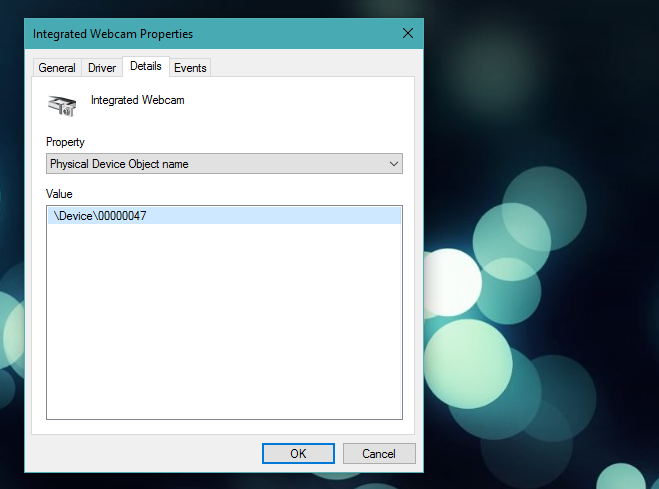
Go to the ‘Details’ page and in the ‘Property’ drop-down, select ‘Physical Device Object name’. In the Value section, right-click the name, and select ‘Copy’.
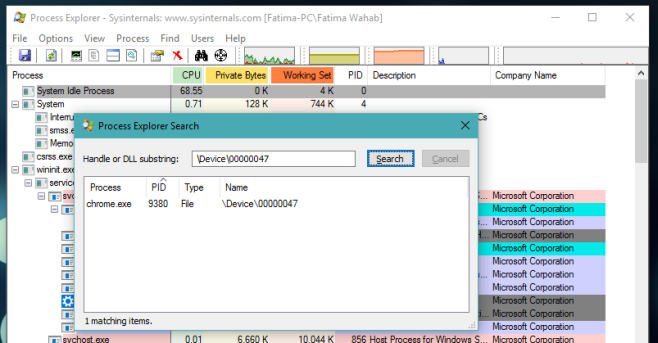
Now, download and install Power Explorer. Run it and hit Ctrl+F. In the ‘Process Explorer Search’ box that opens, paste the physical device object name you copied for your webcam. Give it a few minutes and Process Explorer will show which currently active process is using the webcam.
In the screenshot below, you can see ‘chrome.exe’ as the process that is using the webcam. If you’re dealing with a malicious app, it’s likely going to have a name that makes it difficult to identify which app it belongs to. Use the Task Manager’s expanded/detailed view to look for it.
It’s also worth mentioning that if your browser shows up in the list, the culprit might be a malicious website you have open in your web browser. Web browsers normally ask permission on a per-website basis before letting a website use your webcam but malicious websites will likely have found some way to circumvent this. That’s what makes them malicious.
This method will work in Windows 7, 8/8.1, and 10.

Good information. In today’s vulnerable world we should have this info to block malicious apps.