How To Bypass/Disable Pattern Unlock On Android via ADB Commands
Pattern unlock is one of the many device protection mechanisms available to Android users, and there are quite a lot of people out there who actually rely on said method to secure their devices from unauthorized access. The problem, however, arises in case you forget the pattern that you set to unlock the device. Worse yet, there could be a situation where your friend may have tried to play a prank on you by setting a pattern lock that you are completely unaware of. The question is, how does get out of such tricky situation without suffering any headaches? Seems like XDA member m.sabra has the answer – more than one, in fact. The dev has come up with a couple of very effective computer-based solutions in this regard that let you easily bypass/crack pattern unlock on any Android device. The only caveat in employing both said solutions is that they require ADB to be installed on your computer, and USB Debugging enabled on your device. Although both methods are known to be working with rooted, as well as non-rooted devices, employing them on a rooted device is likely to yield more fruitful results. Past the break, we’ll be taking a closer look at both solutions in detail.

First things first, and you must have good knowhow of installation and use of ADB. If you’re new to Android, then our detailed guide on ADB and all interrelated components could of ample assistance to you.
To toggle USB Debugging on Android 4.0 and higher, navigate to the Developer options on the general settings screen. On non-ICS devices, said option can be found by navigating to the Settings > Applications > Development screen.
Provided all prerequisites are in place, here’s what you need to do in order to nullify pattern unlock on your Android:
Method 1
- Connect your device with the computer via USB cable
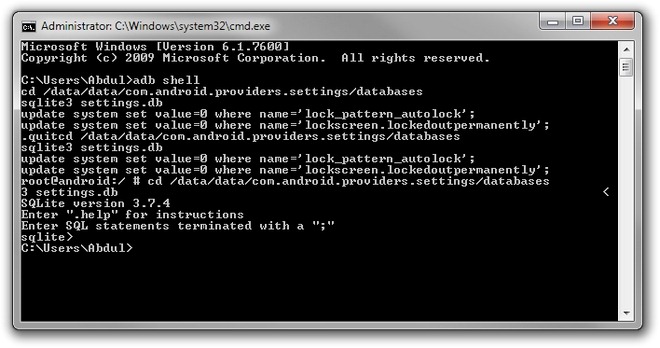
- Open Command Prompt and key in the exact code as displayed below:
adb shell cd /data/data/com.android.providers.settings/databases sqlite3 settings.db update system set value=0 where name='lock_pattern_autolock'; update system set value=0 where name='lockscreen.lockedoutpermanently'; .quit
- Reboot your device
- You may now unlock your device providing whatever pattern you like
Method 2
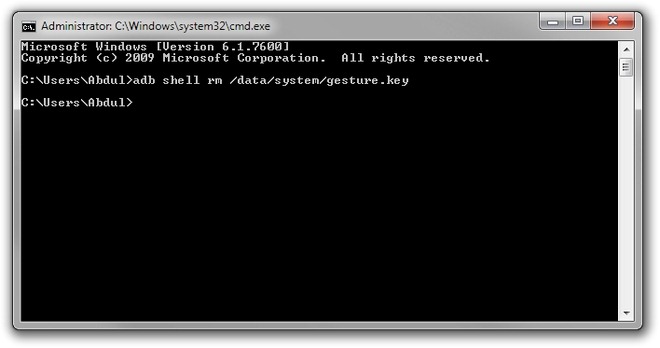
If the above method doesn’t work, try using the following code instead:
adb shell rm /data/system/gesture.key
After rebooting, unlock your device using ay preferred pattern. As evident from the above, neither method disables the pattern unlock. Instead, they just nullify the pattern order on the lock screen.
Both methods have successfully been tested using a combination of HTC Desire Z (running CyanogenMod 7.2) and Windows 7 (64-bit Edition), and a good thing about these solutions is that they work independent of, as well as in tandem with, each other, so no harm in deploying them both simultaneously. Once you regain access in to the OS, head over to the system security settings, reselect your preferred unlock method, and you’re good to go.
Special Note: The purpose of this guide is to help users with employing an effective pattern unlock bypass solution only on their own devices, instead of using it for malicious (read: unethical) purposes. On the other hand, it begets the need to keep USB Debugging disabled on your device if and when not required in order to be on the safe side.

Not working on Android 8.1(Go edition). The first method is access denied while the other doesn’t find that file
ghanta kaam krta hai ye landura
How to enable the USB debugging if pattern is already lost
how can you enable USB debugging when the device is locked
i got device offline
MAN!!!!!
it doesn’t withouth SUPER_USER command????
Do you have any solution for this???????????????????
for those with custom recovery you can use your recovery file manager to remove lock screen pattern or pin .db then it would be gone.
it works on Qmobile to unlock
This requires root permission no?
need to get this off my phone need my info denied access do not want patterns how do I uninstall SAVE MY INFO
lol..how i can enable USB debugging when i forgot my password ???:P
plz help me, htc increible s is too many pattern attempts & my gmail id or pw invalid so
Just reset your GMAIL id and password of the account which you have in your mobile . If it doesn`t work do it using android system recovery
I got broken screen, then the touchscreen doesn’t work, I can’t activate debugging mode, I can’t unlock my phone (locked with pattern) and I want to recovery all my data, how can I do so? I have Sony Xperia V (LT25i).
Both tricks are not working.
I did it but both methods were failed: permission denied.
what should i do?
and by the way usb debugging is on!
This is Really gr8 Help to me….I have Domo Gadget Tablet Slate N9se Device.
I forgot the Patter but I have recover it with help of this Post Thank you much…..
AND I DO NOT LOSE A SINGLE DATA ALSO
HELLO , HI, PLEASE HELP ME IN MY SAMSUNG GALAXY Y I 509, TO UNLOCK PATTERN-LOCK, SO, I FORGOT IT WHAT I SHOULD TO DO ?
First things first, you should learn to type not IN CAPS
thanks! its working only you must have rooted device and enabled usb debugging 🙂
I got permission denied too!
really wish my phone alive again without loose my contents…
T.T~~
THANK YOU SO MUCH!!!!! The first didn’t work but,second one did, but instead of deleting it O renamed it with the command ‘mv /data/system/gesture.key /data/system/gesture.key.bak’
You can add to the confirmed list: Samsung Galaxy S+ with CyanogenMod 9
I tested it but I got permission denied. how to solve
I think, it will work with Rooted Mobiles
by putting this ommand : su
means super user
how would I use this command?
You would instead of ‘cd /data/data…/’ or ‘rm /data/system/gesture.key’ do ‘su cd /data/data…/’ or ‘su rm /data/system/gesture.key’.
same here
you need to enter SUPER_USER command first..
$ su then the described commands.
type
“su” without quotes before the code..
It then will work fine
There is a mode to enable USB debugging using the ADB or other method?
i also want to know
Hi,
No there is not. You need USB debugging to be able to use ADB.