Prevent Mac Apps From Using Internet Connection With TCPBlock
Like Windows, where malicious applications can gain access to network over TCP/UDP protocols, Mac OS X is also prone to such attacks not only from internal programs, but also from external scripts and apps that connect with system through internet. Although Mac OS X’s native Firewall app tries to block all connection requests from external sources, it doesn’t keep a check on internal applications that send requests to connect with internet, or try to communicate over TCP or UDP ports. Whether you haven’t installed a staunch security application or Mac OS X native Firewall settings are too lax, you need an application like TCPBlock. It secures Mac from those installed applications, processes and scripts, which either attempt to surreptitiously communicate with external sources over TCP or UDP ports, or open connections to networks without asking for permission.
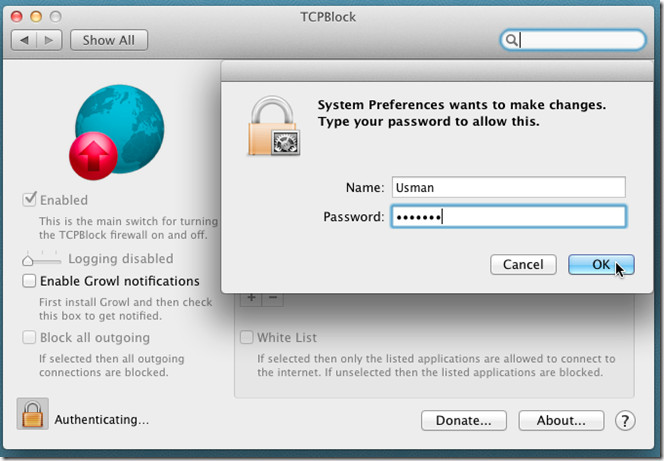
The application comes as a package and needs PKG file to be installed to work. You need administrative privileges to launch the installer. Once installed, reboot your system and launch it from System Preferences. The first step is to unlock the application to block programs which connect with network connections. Click the Lock icon in bottom-left corner, enter the admin username and password to unlock the application.
Once unlocked, you can block all outgoing connections by selecting Enabled option from left side. It allows you to create a White List for applications which are not to be blocked. Enable White List option and click add button to insert applications which you want to insert in whitelist. Apparently, there is no limit defined on number of applications that can be added to whitelist. While creating whitelist, make sure that you’re not adding applications that can provide root access gateway to outside sources.
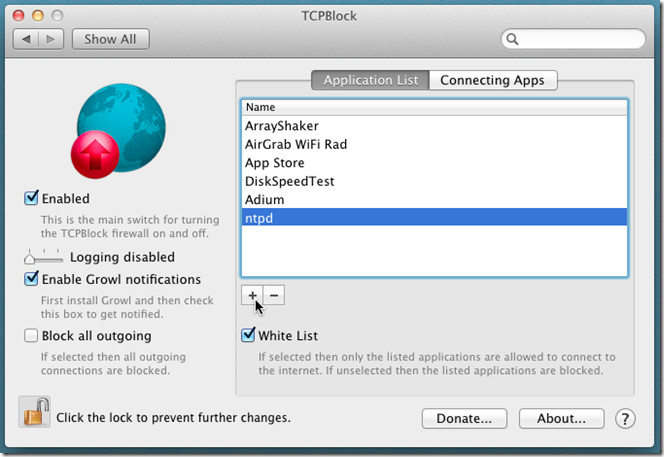
TCPBlock supports Growl notification system. If Growl is installed, check Enable Growl notifications checkbox to enable on-screen notifications for those applications which send connect requests over TCP/UDP ports.
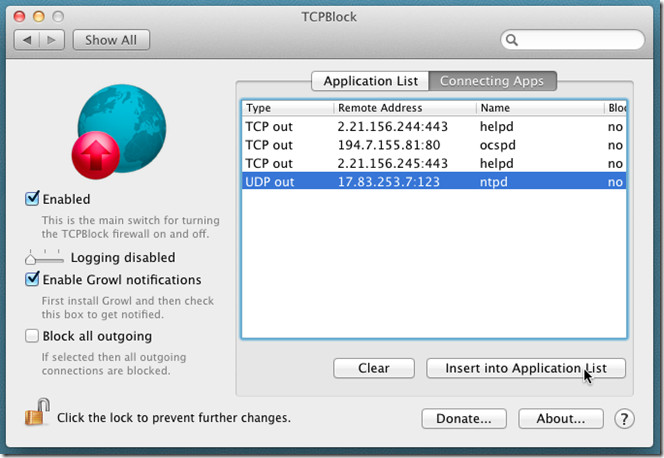
The Connecting Apps tab in main window lets you view applications and processes which are currently trying to connect. It displays the type of communication protocol they are using (TCP or UDP), remote address, Name of process, and Blocked status (Yes/No). You can add the applications which are being connected to remote locations to whitelist from within the Connecting Apps tab; just select the application and click Insert into Application List to send the app to whitelist.
The Block all outgoing option uses an obnoxious approach to restrict connections over TCP/UDP ports. It may block all types of outgoing remote access. This includes all shared connections, applications using data from network locations, cloud services’ desktop apps, etc., During testing, we noticed that TCPBlock has the ability to restrict network location access via Finder as well. Therefore, it’s advised to insert Finder.app in whitelist to easily send and receive data from local network locations. It works on Mac OS X 10.5 or later.

How does this compare to little snitch? Anyone have first-hand experience? I’ve used LS for years to keep potential nasties from doing that.